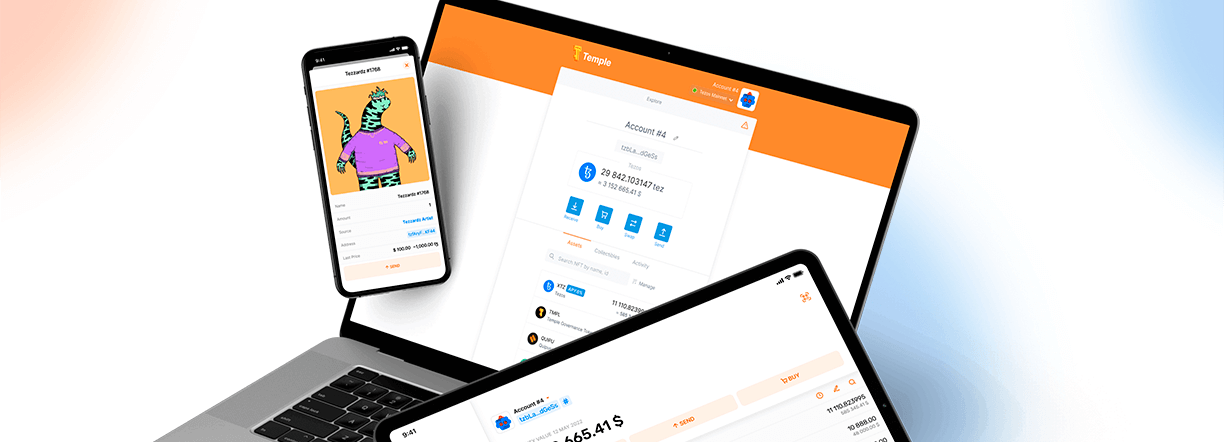
Digital wallets security solutions
Digital wallets take different forms: custodial or non-custodial cryptocurrency wallets, mobile banking or money transfer applications. They all serve the same function: storing and managing user’s financial assets through apps.
Digital wallets face threats related to secure data storage, authentication and fraud prevention. As a result, they have elevated security requirements by combining financial, banking and privacy regulations with platform (web and mobile) specifics.
Digital wallet security challenges
Developers are not cryptographers
Development teams frequently face cryptographic challenges: selecting suitable crypto primitives for the intended purpose, working with cryptographic libraries API, home brewing protocols, and so on.
Digital wallet security is complicated
The security of digital wallets is a gray zone as it's not defined in the single standard. Developers should have extensive experience in both traditional financial security, platform requirements and "cutting edge" technologies.
Compliance with standards and regulations
Digital wallets are not subject to standards and regulations such as PCI DSS and PSD2, but as financial apps, they should aim to be compliant as the landscape is changing constantly.
Mobile & web platform security threats
To protect stored financial data, prevent unauthorised transactions, and stop malicious users, digital wallet components require application security and data security measures.
Fundamentals of secure wallets
Reliable cryptography
By integrating cryptographic libraries with proper cryptosystem design, we unify encryption across iOS, Android and web platforms, reduce external dependencies, and decrease attack surface.
User-friendly security
Users expect their wallets to be secure by default. Applications should notify users of existing limitations, provide security warnings and educational tips, and provide guidance on how to use the app securely.
Multi-layered defenses
Platform-specific security controls such as user authentication, remote device attestation, secure data storage, as well as anti-abuse and anti-fraud should work together and cover the whole data lifecycle.
Address digital wallet security challenges
// Relevant products
Acra
A DATABASE SECURITY SUITE
Themis
A CROSS PLATFORM CRYPTO LIBRARY
// Consulting
Security assessment
SSDLC
Cryptography engineering
Have a question? Get a human to answer it!
How we make a difference
Cryptographic expertise
We have vast experience in improving the security of digital wallets and know how to aid your team. Your developers do not need to know cryptography to protect the data. We suggest suitable cryptographic primitives, select libraries, configure API and ensure that the cryptographic layer is covered with tests.
Pragmatic applied security
We ensure that implemented security measures adhere to the defence-in-depth approach, are designed efficiently, are appropriate to your risk and threat model, and fit well with the application specifics. Also, security should not degrade the user experience.
Security peace of mind
Security-aware digital wallets comply with privacy regulations, reduce the chances of security incidents and data leaks, de-risk the due diligence process, and reassure your users that their data is protected.
You do features, we nurture security
Your developers continue to create new features, while we gently educate and nudge them to the "secure side", shifting security left, and maintaining security processes and documents.
For innovators, by innovators
We've started Cossack Labs to develop new tools and methods for protecting the data and enabling novel solutions to emerging problems — so that at the edge of your innovation, you’ve already got fitting tools handy.
Contact us
There are many ways we can help: with our products, bespoke solutions, and engineering services. Leave your contact information to connect with our team:
Relevant blogposts
Smart contract security audit: tips & tricks
Smart contract security audit is very different from traditional application security audit. Smart contracts are immutable, they interact with each other and transfer user funds between accounts. Unique threat landscape brings unique challenges.

Crypto wallets security as seen by security engineers
How to build secure crypto wallets, analysing issues found during crypto wallet security audits.
Exploring security vulnerabilities in NFC digital wallets
NFC-based devices, such as mobile digital wallets, contactless smart cards, and security keys (hardware authentication devices), are exposing users to NFC vulnerabilities in encryption, replay and side-channel attacks.