Cryptography engineering
Cryptography has historically been viewed as one of the hardest-to-get-right, yet most robust defenses against data leakage, tampering, and misuse.
Rolling your own crypto is a sin unless you're a cryptographer. Even then, it's still a bit of a sin. We know limits to our knowledge, and we understand where to roll, where to pick existing stuff, and how to adapt it to your product.
Implementing cryptography
is like dancing on thin ice
False sense of security
Any persistent engineer can invent a security system so clever that they can't think of how to break it. All these systems get broken, of course.
Competence is rare
To build secure cryptographic systems, your team must have specific competencies in building, reviewing, and breaking such systems. Competence is rare, and the ability to find competence is even more rare.
Real-world cryptography is hard
Along with strong security guarantees, cryptography brings unique technological challenges when it is used in the real world. Marrying cryptography, performance, and user experience in a product is challenging.
Cryptography misuse
Repurposing "something similar" leads to detrimental effects—cryptographic protocols are built for certain use cases, risks, threats, and environments. Reusing them blindly is a recipe for disaster.
What it takes to do crypto-based security
Cryptographic design
Many products involve professional data security specialists from the start of the design phase to ensure that product decisions take future cryptographic subsystem into account.
Correct verified implementations
Implementing cryptography is hard and requires knowing what to do yourself, what ciphers and libraries to use, and what to avoid.
People with relevant experience
Even if something is implemented, verifying it and bringing it up to the desired level requires design and implementation review by qualified engineers.
Cossack Labs' difference in cryptography engineering
Applied experience
We make sure that implemented security measures adhere to a defense in depth approach, are well-designed, meet your risks, and fit well with the application architecture.
Trained cryptographers
Our extensive cryptographic and software engineering experience enables us to match security and cryptography to a product experience.
Real-world, factored in
Even the best security controls won't work if implemented incorrectly. We conduct a security review of each component, the overall application security posture and specific compliance requirements.
Our mission is simple.
We help you focus on serving your customers better, while relieving your team from security engineering pains and making your users confident that their data is safe with you.
Contact us
We can provide a wide range of cryptography engineering assistance—from handling zk-SNARKs to building end-to-end encrypted mobile apps.
If you need novel crypto schemes, cryptographic design validation, or cryptocode audit—our engineers can help you.
Relevant stories and posts

Cryptographic IP protection for AI/ML product
Protecting unique IP (ML models) against leakage and misuse using multi-layered encryption on ephemeral keys.
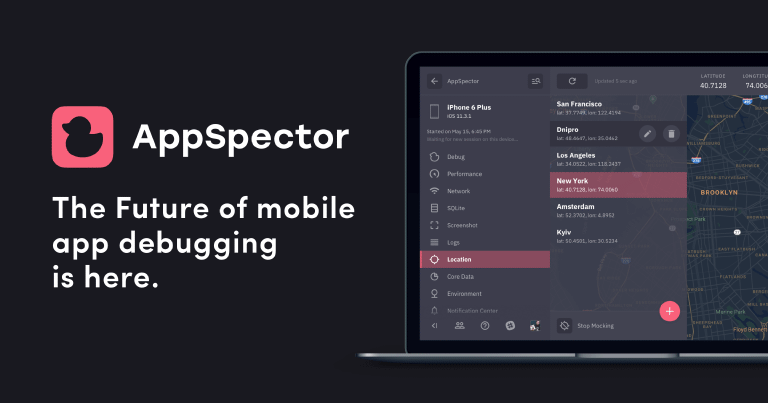

End-to-end encryption for remote debugging tool
Data encryption and isolation in AppSpector for securing mobile development and helping digital nomads around the world.

Secure search over encrypted data
What is searchable encryption and how to perform secure search over encrypted data.