Perimeter security: looking back
Over the years, the Internet has evolved, and complex systems facing the Internet have evolved too.
Traditional security methodology to defend these systems was to build strong walls around your most valuable assets: build a castle and hope it stands against the external adversary. We’ve invested into firewalls, data leakage prevention systems, intrusion detection of all sorts.
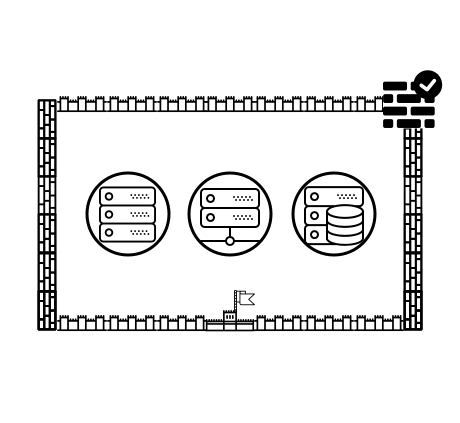
And what’s behind these walls? Whatever it is, it’s protected, we’ve thought for a long time.
Isolation and perimeters are not top priority anymore
Stand-alone perimeters do not exist anymore:
companies rely more and more on external SaaS services and shared assets
computation and storage are quickly moving to the cloud
employee location is virtualized, networks are more of routing state than actual attribute
direct access from internal applications to external resources is a standard thing now
The problem is, everything is on the Internet now and is so deeply integrated that things are not isolated anymore:
any internal software has update mechanisms which will try to punch a hole in the firewall to call home
modern web development led to a state where every web page embeds resources from all around the Internet, and frequently in an entirely uncontrolled manner (remote fonts loading? blind JS embeds?)
internal infrastructure is actually built on top of Internet now, and frequently isolation is just not there
containers, blindly installed 3rd party packages, package managers with dependency validation bring unknown code into your infrastructure
malware, which proliferates everywhere, exploits mostly legitimate communication channels and is well-armed with covert communication techniques
insider risk is now considered to be as significant as external risk: whether it's malicious or just a mistake, the result is the same
Even the meaning of network assets has changed: 80 and 443 are now endpoints or tunneling ports for (almost) everything, ports are not so tightly bound to services anymore.
So, although physical metaphor from the middle ages sounds very appealing, it is now evident more than ever that perimeter security has lost its prominent meaning and needs to evolve into all-encompassing security.
Understanding perimeter tools
Firewalls: firewalls restrict access based on various connection properties, matching these properties to sets of rules, and letting in some of the packets and refusing the others. Infrastructure-wise, there are different firewalls on each level of OSI model, from layer 3 (where packets are inspected) and all the way to high-level behavior on layer 7.
Moreover, firewalling techniques for the data link layer are getting more and more adopted outside its rather obscure ISP-level popularity.
Intrusion detection system: the logical continuation of firewalling is inspecting for signatures and signs of suspicious activity. IDSes are tools which inspect traffic, try to detect suspicious behavior or artifacts, which should not be there, and block it or notify someone.
Authentication: over time, authentication has evolved from simple “who’s that and where’s your secret” to a number of sophisticated protocols, preventing possible passive/active MiTM attacks, utilizing public key cryptography, transport encryption and increasing overall security guarantees for legitimate users.
Data leak/loss prevention: DLP allows controlling network perimeter for signatures of sensitive chunks of data, thus controlling what data leaves secure perimeter.
These are static defenses: walls. Static defenses protect well against known threats. But most modern threats are unknown: malware, APT attacks are barely detectable, describable and preventable.
We work with companies on demanding markets.
Read how we protect data in critical infrastructure.
Components of modern resilient security system
Perimeter tools: evolved and extended
Despite a popular trend, we’re not advocating “perimeter is dead” approach and do not advise you to abandon your firewalls. The statement is - “perimeter security is not enough”. But what is?
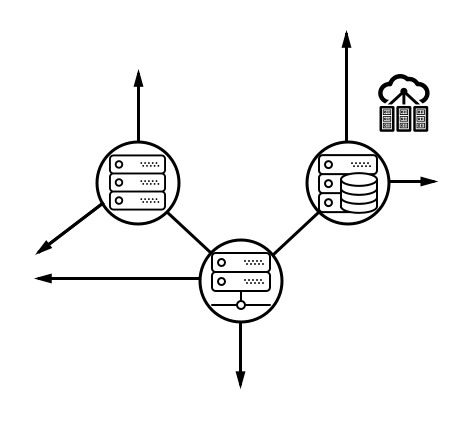
In strong, resilient infrastructures firewalls are used to limit access of attackers on every step: between any two servers inside the trusted infrastructure, firewalls should allow only explicitly allowed traffic.
Intrusion detection should not only be bound to the perimeter but connect sensors from every server, perform log analysis from the internal monitoring system and try to catch consistent patterns. Intrusion detection makes the most sense when combined with proper firewall implementation on every step so that there are strict rules what is and what is not considered an unusual behavior.
Authentication is even more important right now: using modern authentication algorithms, managing certificate-based authentication via strong PKI infrastructure, managing and rotating secrets securely and safely distributing keys is a minimal baseline to make authentication the useful pillar of general security.
A wise, but rarely implemented choice is to consider everything that has contact with data from the external world to be trusted as little as possible.
Achieving resilience is expensive
Previous suggestions might feel like having a 10x administration and maintenance overhead! Is it practically achievable? Yes, if you strive to improve your system administration as much, as security:
Configuration automation. Labor of maintaining configurations multiple security tools is feasible when configuration and its distribution is automated and maintained in a centralized, versioned state. Good examples are tools like Chef, Ansible, and SaltStack. Through configuration automation, there are a few security properties to be achieved:
Ruleset generators. Firewall and app firewall rules are not the best things to be written by human beings. Either as a part of configuration automation or as a separate process,- it’s wise to generate configurations programmatically, ensuring correct syntax and parameters validity based on their metadata instead of relying on copypasting.
Asset enumeration. Secure assets have their centralized descriptions and based on their roles security parameters are assigned automatically, for example, aforementioned rulesets for firewalls and authentication systems.
Role-based authentication. In sophisticated technical environments, as little as possible should be bound to each unique credential. Moreover, constantly rotating keys and changing privileges of the same group of people increases the risk of mistake – a mistake that would lead to a fatal breach. Using role-based authentication everywhere allows certain users (or certain keys) to be able to unlock narrowly limited privilege sets, just enough to execute the certain goal.
Encrypt anything important. Really, encrypt everything. For modern processors, symmetric encryption is cheap. Decent implementations are very fast. There's only one complication:
Manage keys properly. Store keys apart from the data, rotate timely, avoid one-key-fits-many-locks, think of it as if the infrastructure surrounding encrypted data is compromised already. Make picking the keys a tough job.
Compartment trust tokens from the external-facing systems. If anything facing outside world is considered low-trust, make sure there are no keys to anything valuable, other than credentials to connect to internal, more trusted systems in a controlled, limited way.
Data is the new perimeter
Specifically, apps processing, transferring and storing sensitive data are the new perimeter themselves. Sandboxing and containerisation, encryption with owner-bound trust, data isolation some of the most obvious next steps in leveling up the data security.
Building modern security systems means moving as much defense tooling as close to sensitive assets as possible.
This is exactly the reason why our company is so focused on cryptography: it should happen virtually on every step in modern applications working with sensitive data, yet the form factor, use-cases of tools used to defend data in modern applications is next to awkward right now. Some of our tooling is aimed exactly to solve this.
Further reading: ideas, opinions
Everything will be broken by Eugene Pilyankevich
Lessons learned at RSA 2016
The perimeter is dead: welcome to data security future: although the title is misleading, the ideas about what really is a defendable asset are important.



