Custodial or non-custodial cryptocurrency wallets, money transfer platforms, or banking mobile applications — regardless of their forms, digital wallets are expected to provide secure storage of users’ financial assets. Having gained popularity, digital wallets became a target of malicious actors, bringing financial losses and reputational damage to many companies and their users. Yet the system is as strong as its weakest link — and it’s often human behaviour that becomes the first victim to adversaries.
A diverse threat landscape should be addressed with fraud detection-and-mitigation solutions tailored to the features of digital wallets.
In this post, we’ll explore the recent cases of digital wallet fraud from a security engineering perspective and discuss the engineering solutions for building an effective anti-fraud system. We will focus on mobile digital wallets mostly, with some examples of web and hardware wallets.
- Digital wallet fraud: Expensive cases
- Mobile wallet fraud: What you need to know
- How to build an anti-fraud system
- How to prevent digital wallet fraud by educating users
- Anti-fraud measures: Understanding trade-offs
- How to work with security researchers
- Conclusion
This blogpost is a part of the “Digital wallet security guides”: Read the articles Crypto wallets security as seen by security engineers, Exploring security vulnerabilities in NFC digital wallets, Digital payments security architecture guide.
1. Digital wallet fraud: Expensive cases #
Learning from other people’s mistakes is always a smart choice when it comes to building secure and reliable products. So let’s discuss some recent cases that have made headlines from the opposite side of the spectrum — one on human side and one on development side.
MetaMask: Targeted phishing campaigns #
MetaMask wallet case shows how a well-planned phishing campaign has affected thousands of users and thus is a good example to refer to.
The cybercriminals used fraudulent websites, phishing emails/messages, malicious browser extensions, and social engineering, aiming to deceive MetaMask users into revealing their credentials.
MetaMask has issued a comprehensive guide on protecting digital wallets from attackers, explaining how to protect a seed phrase, manage browser extensions and recognise phishing attempts. MetaMask is a good example of communication with users. Their in-app error messages are user-friendly, guides are simple, recommendations are usable: “be cautious, use 2FA, ensure you are on the real MetaMask website”.
Human behaviour plays an important role in ensuring the effectiveness of a strong defense against fraud.
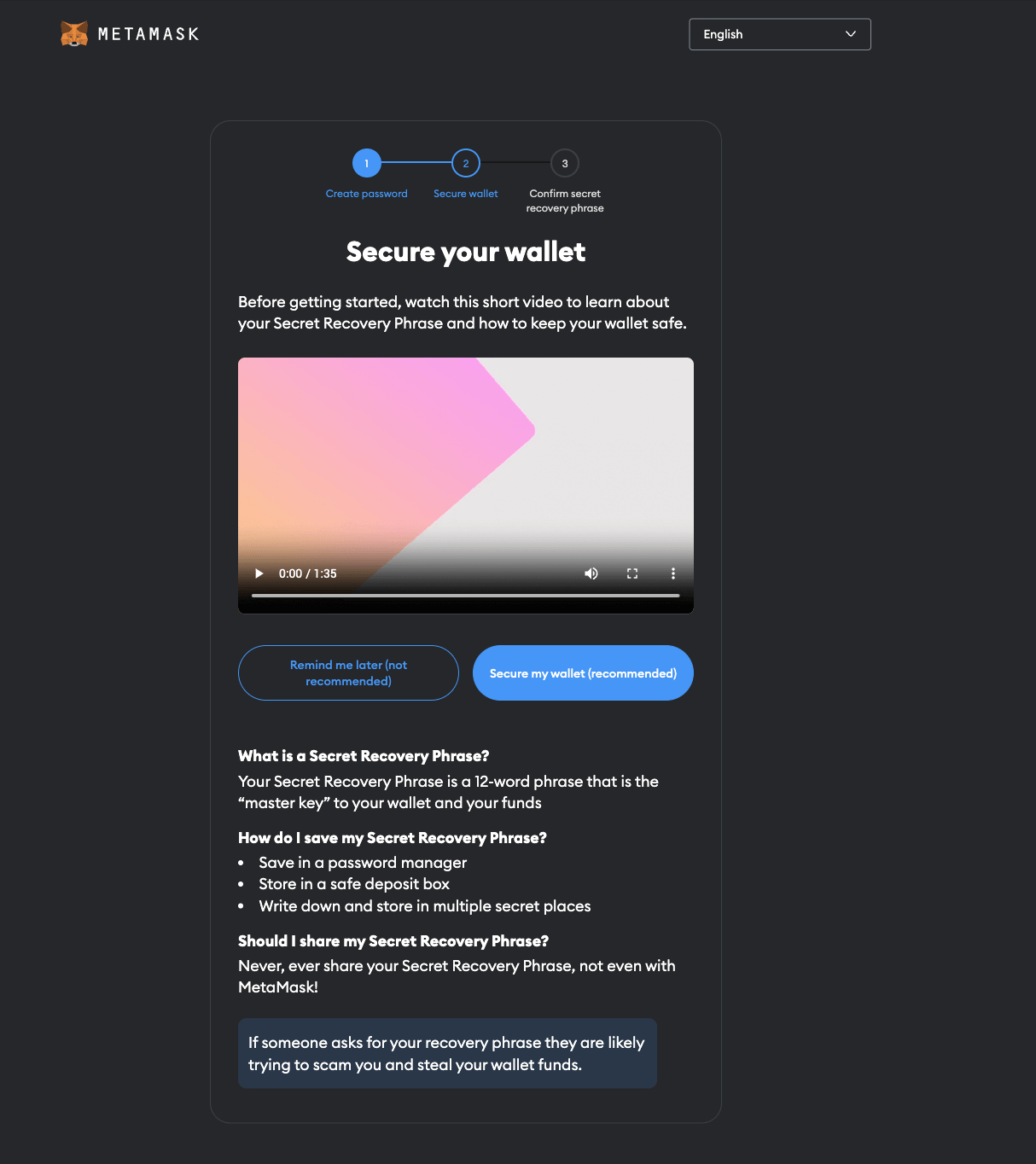
MetaMask educates users about protecting their secret phrase.
Users can secure their wallets by being vigilant:
- Never share their secret recovery phrase,
- Double check the website before inputting sensitive information,
- Keep an eye on their payment information.
Slope Wallet: Alarming software bug #
Slope is a digital wallet that works with Solana cryptocurrency. In September 2021, users reported losing their funds due to suspicious activities. Investigations revealed that the private keys of ~8000 wallets were compromised, allowing cybercriminals to transfer funds to their own wallets.
The real root cause had nothing to do with cryptography or Solana blockchain itself, rather a security flaw in Slope client application architecture. The users’ private keys were transmitted to the Slope server monitoring service.
Thousands of users’ private keys were found in the logs.
The Solana case was a big one, having engaged a great number of engineers in investigation, which finally revealed the real cause of the accident — a simple software bug, overlooked by developers and auditors.
According to SolanaStatus tweet, the bug was in the software used by “several software wallets popular among users”.
2. Mobile wallet fraud: What you need to know #
Mobile wallet fraud refers to any unauthorised or fraudulent activity, occurring within a digital wallet. This includes illegal transfers or withdrawals, tricking users into making unwanted actions, getting unauthorised access to the wallet, or any other type of financial crime committed through an e-wallet.
Social engineering #
Phishing is a type of social engineering, a psychological manipulation to trick users into revealing their secrets. Attackers send fake emails, text messages, or even engage in phone calls (vishing) that appear to be from a legitimate source, such as a customer support team of the digital wallet. The messages typically ask users to click on a link, and enter their credentials, which the attackers then use to gain full access to their digital wallet account.
Another scam example is generating fake news. Attackers create fake news about a project or token, then once it gains popularity, they dump tokens and make profits.
Malware attacks #
These have to do with the use of malicious software, such as keyloggers or spyware, to capture users’ credentials. This information can be used to access the user’s digital wallet account and make fraudulent transactions.
Both iOS and Android are susceptible for keylogging attacks, trojans like Vultur, or even remote jailbreaks like Pegasus.
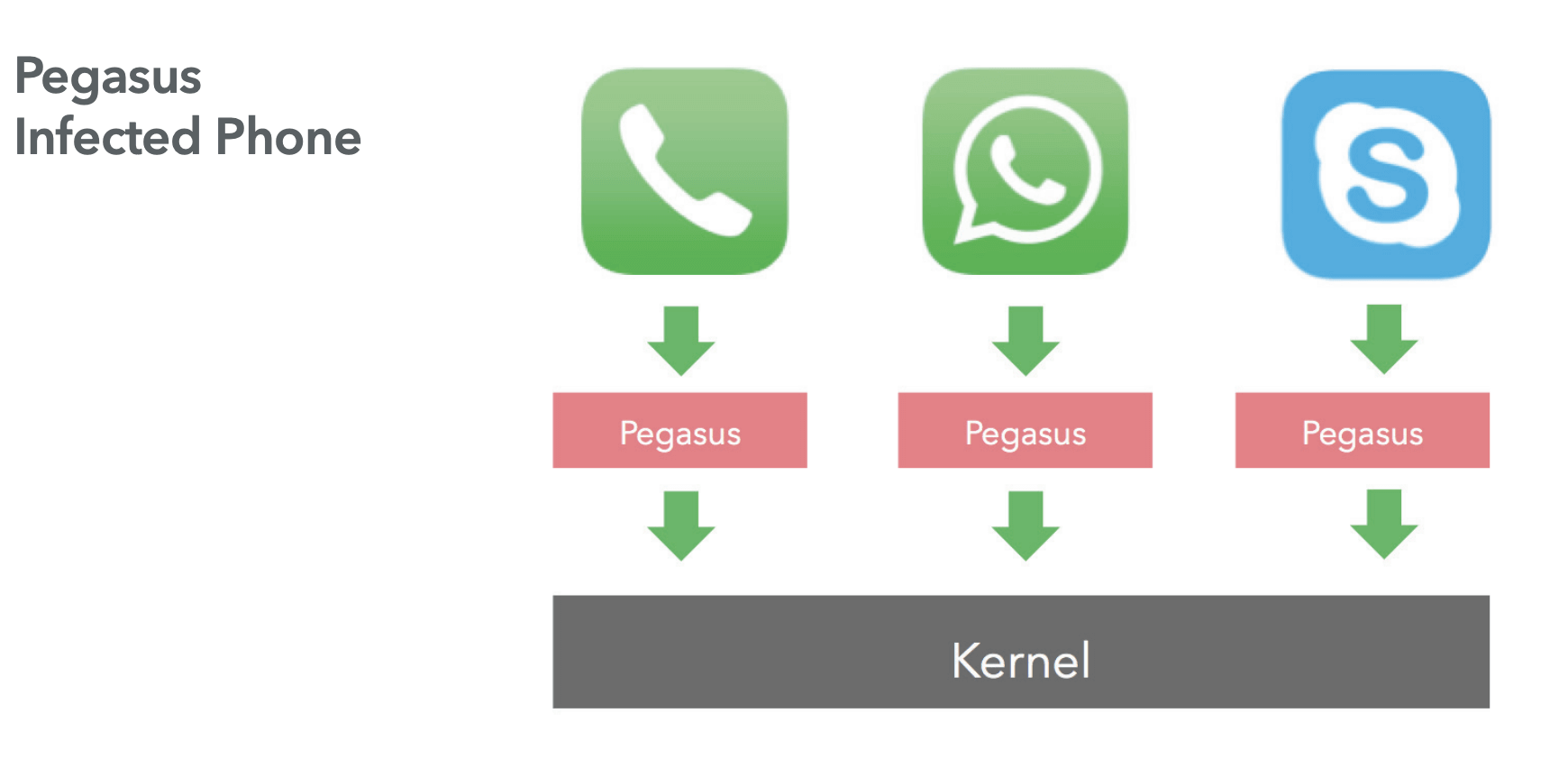
A screenshot from “Technical Analysis of Pegasus Spyware” by Lookout back in 2016.
SIM swapping #
Attackers convince a user’s mobile carrier to transfer their phone number to a new SIM card. This allows attackers to receive the user’s two-factor authentication codes and gain access to their digital wallet account. SIM Swapping attacks happen more often than you think, leading to $68 million in losses in 2021 in the US only.
Stolen hardware cards #
Smart cards are often used as hardware wallets. In case a card is lost or stolen, an attacker can link it to their digital wallet account to make transactions and withdraw funds. To avoid this, a smart card should be protected with a strong pin code or biometrics.
Practical application security focuses on reducing financial loss rather than simply completing checklists.
Evaluate your solution with our engineers.
3. How to build an anti-fraud system #
Protecting customer assets and avoiding financial loss is of essence for any fintech company. When being trusted with customer’s money, building an effective anti-fraud system becomes not only a part of corporate survival strategy, but responsibility towards its customers. Well-designed anti-fraud controls will help prevent fraudulent activity, detect, flag and stop suspicious behaviour.
Anti-fraud is a complex system that needs to be integrated correctly and tailored for each specific wallet to support the “normal” user behaviour.
3.1 Preventing fraud proactively #
Building an anti-fraud system involves several steps: analysing user behaviour, and making assumptions about what is “normal” and “abnormal” behaviour, collecting behavioural events from mobile apps and server-side, calculating risk scoring based on events, limiting access for suspicious users, and blocking malicious users.
Many vendors offer user analytics and event analytics solutions (SIEM, UEBA), but sending some queries to the backend and performing simple statistical computations can be a simpler and more efficient way of preventing fraud.
Understanding user behaviour #
First, understand risk and threats for the digital wallet, and how a typical user flow looks like. Do users use your wallet daily? Will a user switch between iPhone and Android apps during the day? Is it common to send hundreds of transactions during a month, or a week, or a day? Understanding what is “normal” helps define how things might go wrong.
Some companies build lean, dedicated anti-fraud engines within their product, while others offload it to a bigger User (Entity) Behaviour Analysis (UBA and UEBA) solution, that includes real-time security analysis and predictive information, enabling proactive threat prevention.
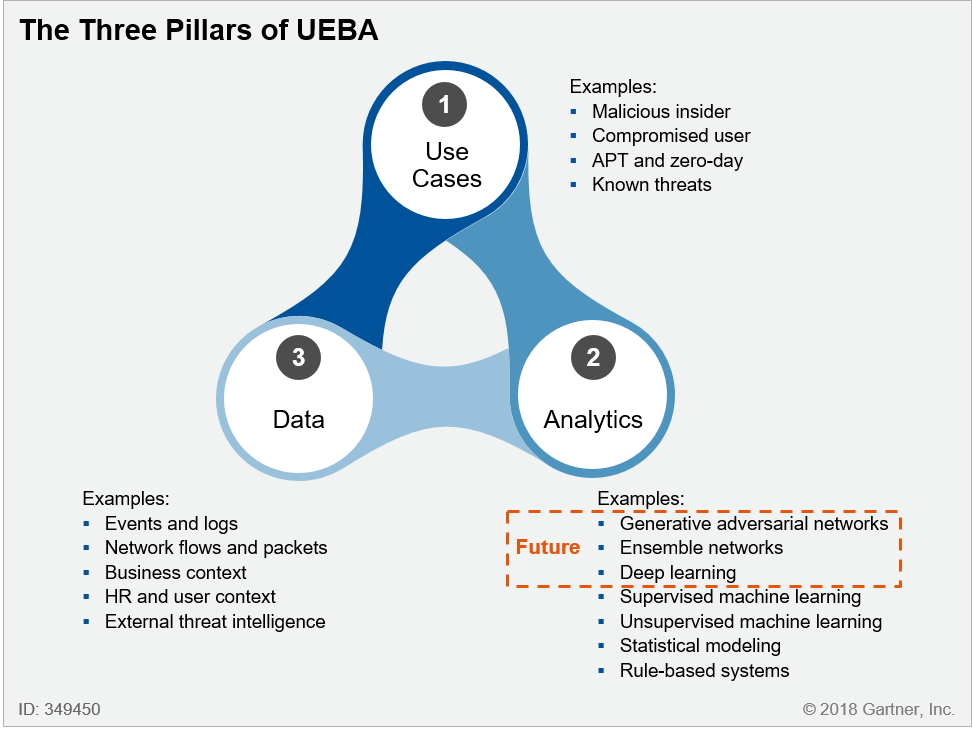
UEBA systems have gained popularity since 2015, see Gartner research
Gathering events #
Gathering events can provide valuable insights into user behaviour. In some cases, a mobile app could be a “source of truth” for security events. Some examples are:
- Is the app being debugged now?
- Is the app being opened on a jailbroken / rooted device?
- Is the user unable to authenticate using FaceID multiple times?
- Is the date/time being manipulated now?
- Does the user tap too many buttons or enters weird strings (“monkey testing”)?
Gather these events, perform protective action in the app (for example, ask the user to re-authenticate), and send these events to the backend securely.
In many cases, the mobile app itself doesn’t have enough information, but the server-side does:
- How many active sessions does the user have currently?
- Does the user switch between different mobile devices during a short period of time?
- Can the user perform dozens of transactions suddenly?
Make sure to sign or encrypt the analytics events and disguise them within other data fields, as connectivity between the app and the server can be disrupted or interfered
Calculating risk scores #
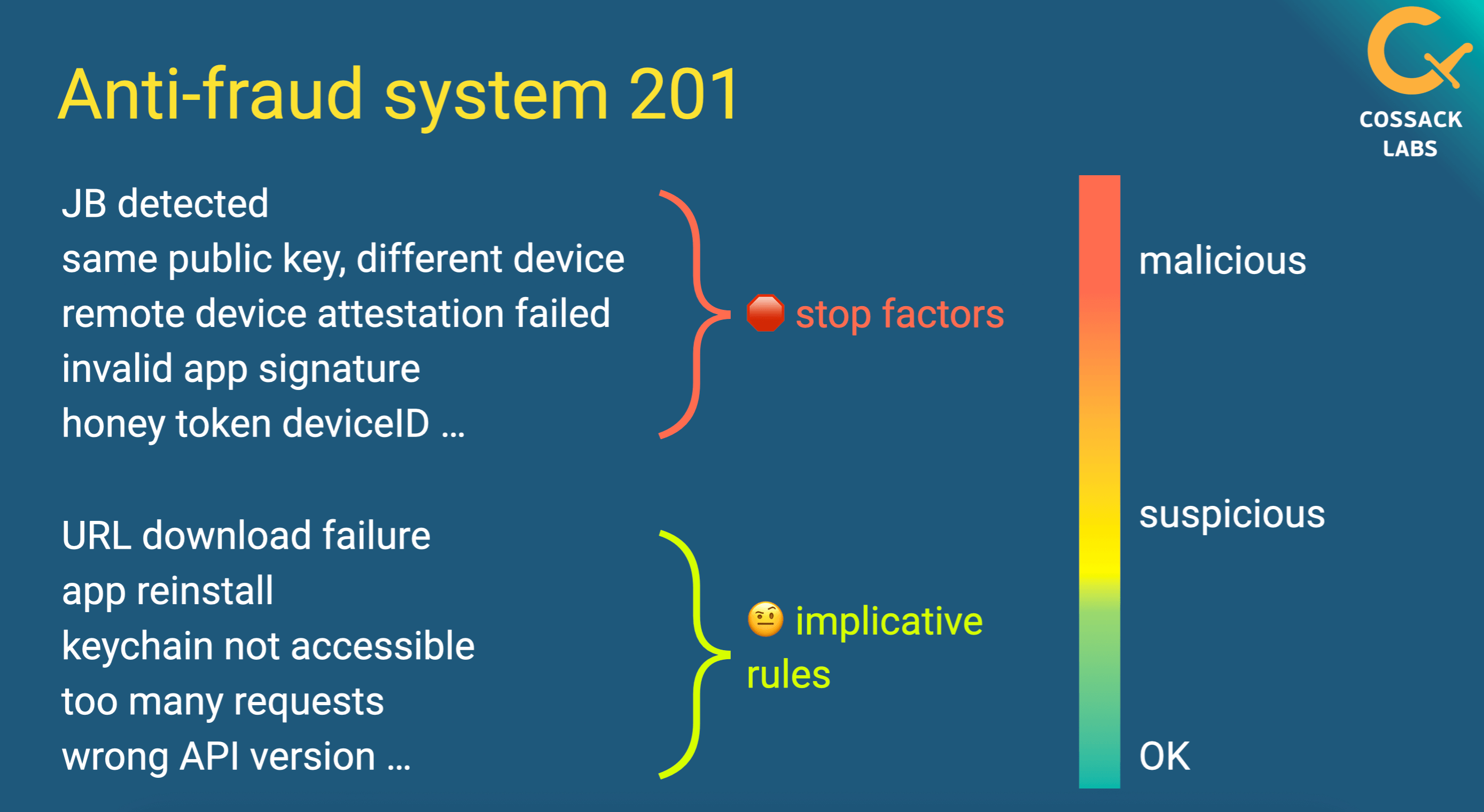
Calculating user risk scoring can help identify suspicious or malicious users. Assign risk scores for the collected events, and treat some events as “stop factors”.
For example, if a user attempts to log in multiple times with incorrect credentials, their score could be increased, and access to their wallet could be restricted.
A screenshot of a talk by Cossack Labs Head of Security Engineering Anastasiia Voitova about Cryptographic protection of ML models. It explains building the anti-fraud system in a mobile app that processes valuable ML models. Video is available.
Limiting access and blocking users #
Define different levels of reaction: suspicious users and malicious users. There is a high chance of false positives as no analytics system is flawless, and because user behaviour might change.
If a user accumulates a certain amount of risk points, consider them suspicious and restrict the access. If a user logs in from an unknown device or location, for example, the system may request more verification before allowing access to their wallet.
However, if the user’s risk points exceed the threshold, or if any ‘stop factor’ event occurs, this user is more likely to be a malicious actor. Once identified as malicious, user’s access to their wallet should be restricted or revoked. It is important to ensure that the system can quickly and accurately identify and respond to potential fraud.
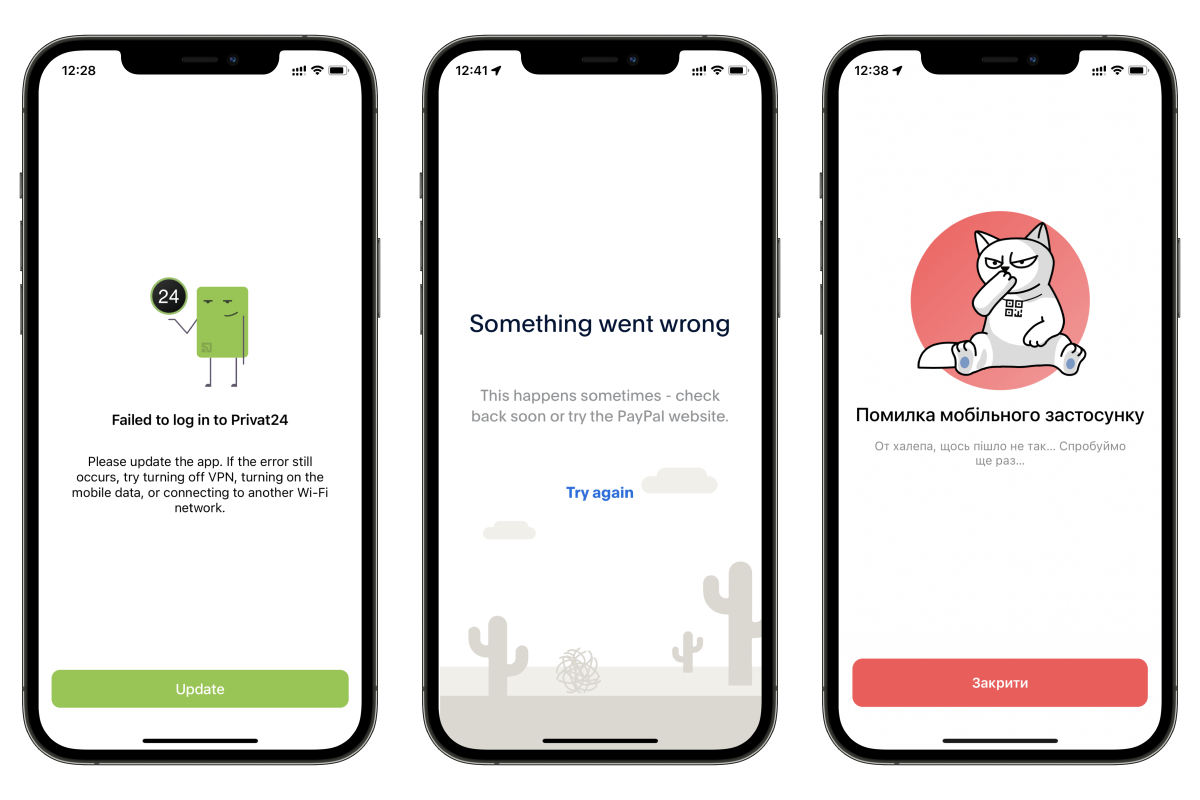
How different banking applications respond to a Man-in-the-Middle attack when TLS certificate pinning is enabled.
3.2 Enabling remote device attestation #
Remote device attestation is the process of verifying the integrity and trustworthiness of the device. This technique is used to distinguish between a legitimate and compromised device by gathering, measuring and verifying the device’s unique properties at the remote endpoint.
Intentional or unintentional modification of vendor-provided operating systems and device hardware can weaken built-in security controls making a device an attractive target for an attack. Compromised devices are associated with a high risk of fraud and leaked user credentials.
Using native APIs: DeviceCheck and PlayIntegrity #
Using APIs that are native to iOS and Android for remote device attestation is the best choice. iOS supports DeviceCheck API and Android supports PlayIntegrity API (recently SafetyNet became deprecated).
To get the most out of the app, device attestation should be performed not only at application startup, but also before the users execute sensitive operations.
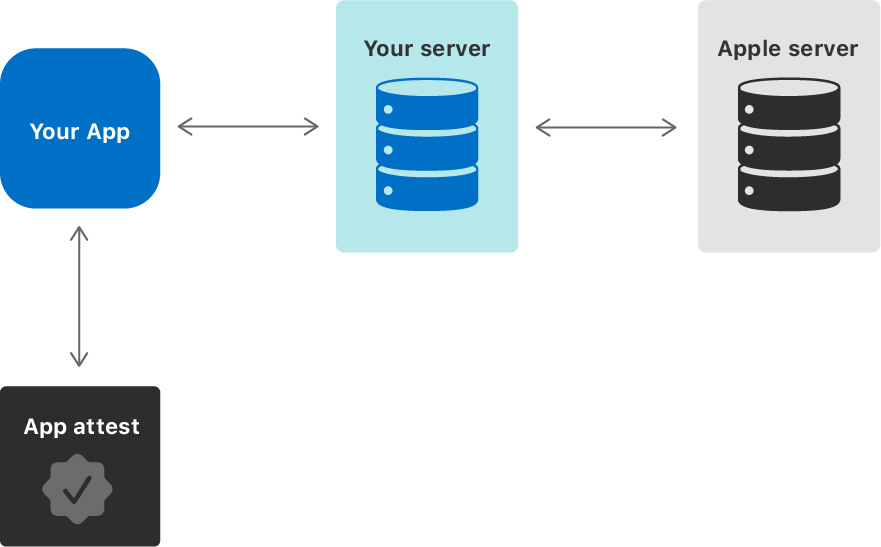
Apple’s AppAttest and DeviceCheck services provide information that developers can integrate into an overall risk assessment for a given device. Image by Apple.
Blocking apps installed not from official stores #
Official app stores provide a safe experience for users as the apps offered meet security and quality standards.
The attack vector for sideloaded apps is very wide: from phishing to requiring permissions to user sensitive data (e.g. collecting information for fraudulent activities). The malicious app can also install a keylogger on the device to steal user credentials. This is exactly what Vultur did by abusing the Android’s accessibility feature.
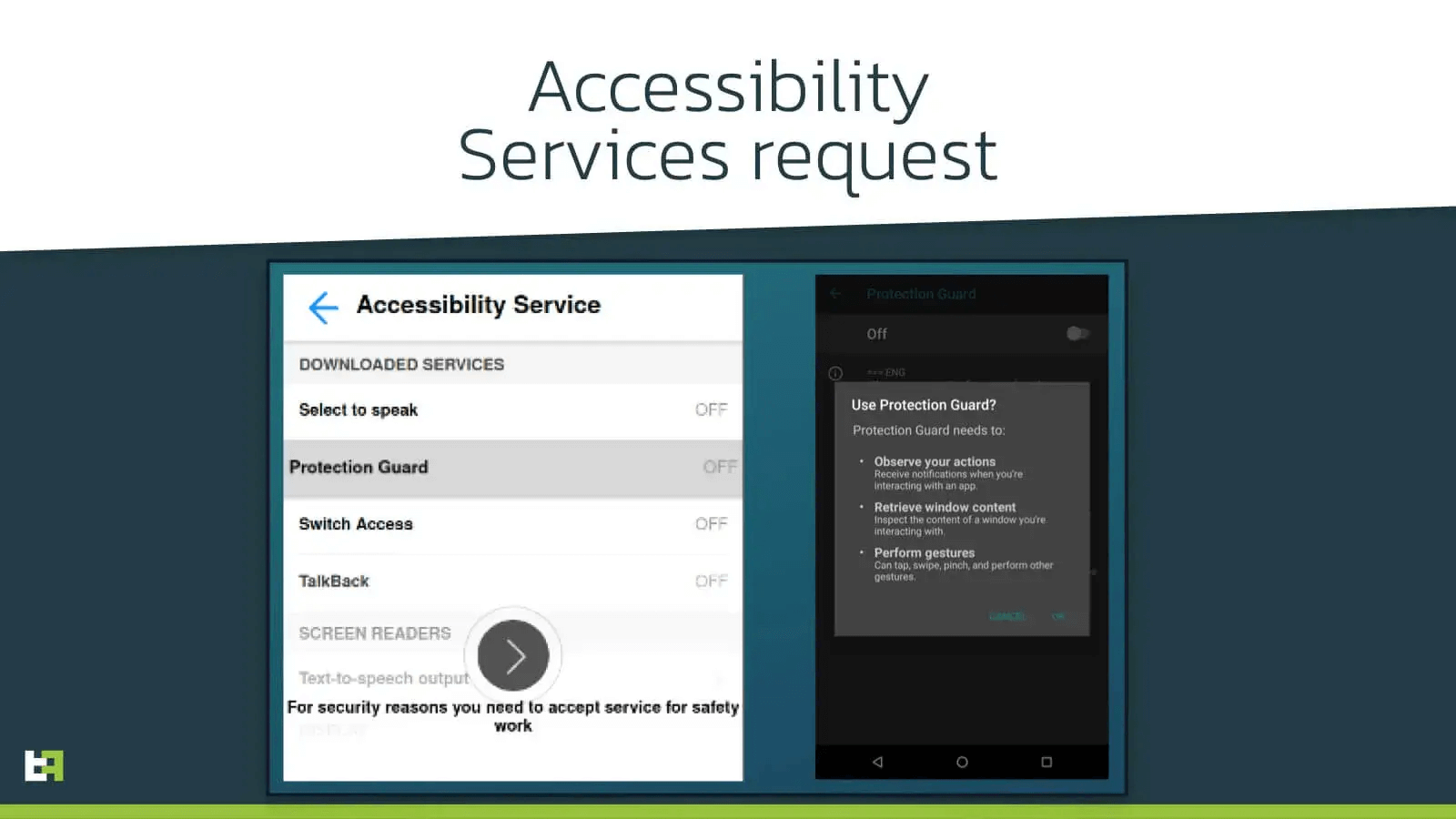
The malware hides its icon and abuses the OS services to get all the necessary permissions to operate properly.
By downloading applications outside the official app store users risk installing malicious or vulnerable software that can be exploited by fraudsters.
Remote app attestation verifies if the app was installed from the store and confirms its integrity. To reduce the risks of fraud and API abuse, the apps installed not from the official app store should be blocked.
3.3 Authenticating and re-authenticating #
Authentication is the process of verifying the identity of a user. It is the first line of defence against fraud. Choosing the appropriate authentication methods depend on the precise use case.
Local authentication #
The app verifies the user identity locally. Typically, it’s a single factor authentication: either enter the application password or use biometry (FaceID, TouchID).
The app must reject weak and popular passwords and apply corresponding password policies. Refer to NIST SP 800-63B to learn more about authentication factors and current rules for “good passwords” (they should be long).
Passwords must be hashed with the appropriate password-based key derivation functions, like Argon2, and never stored directly in plaintext, even in Keychain/Keystore. Refer to the OWASP Password Storage Cheat Sheet to learn more about KDFs.
Biometric authentication provides a seamless user experience. The best way to integrate it in the app is to enable biometric protection for Keychain/Keystore that stores the user password.
Biometric authentication, if any, is not event-bound (i.e. using an API that simply returns “true” or “false”). Instead, it is based on unlocking the keychain/keystore.
A direct quote from security requirement MSTG-AUTH-8 from OWASP MASVS v1.5.
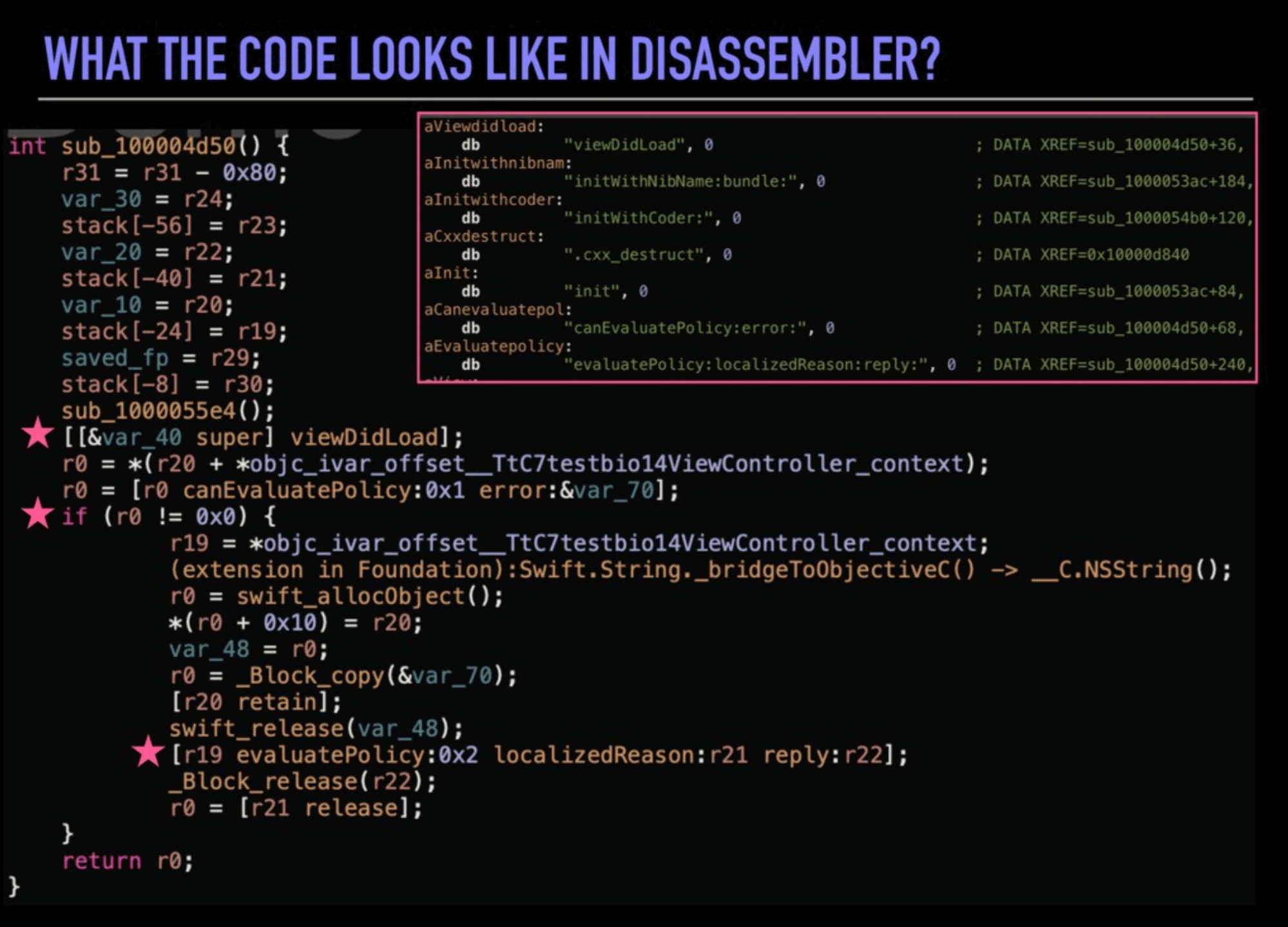
A screenshot from Julia’s Mezher talk “Secure Authentication: Are you doing it right” shows how easy it’s to bypass biometric authentication on iOS if it’s not bound to Keychain access.
Remote authentication #
Remote authentication takes place when the app sends user credentials to the backend.
Wallet developers should consider the new PAKE algorithms instead of sending the plaintext password over TLS. OPAQUE can verify a password without revealing it, though it requires more calculations and network requests. Refer to Soatok What We Do in the /etc/shadow post for more details about PAKEs and passwords in general.
When possible, multi-factor authentication should be used: MFA minimises the risk of account compromise. For example, password authentication can be combined with one-time tokens, like push notifications or TOTP.
Users receive authentication tokens upon the initial login, serving as a digital identifier. Authentication tokens should be present in each request and have a short TTL, limiting potential risks if one is ever compromised.
Good authentication could be tricky to design and implement: check OWASP MASVS V4 Authentication and OWASP ASVS V2 Authentication sections.
3.4 Integrating KYC and AML #
While KYC and AML focus on compliance and risk management (customer identification and prevention of transactions that are suspected to be motivated by money laundering), they rely on similar security controls and involve PII data about the customer.
So, whatever the anti-fraud mechanic is being designed, once KYC/AML controls are in place, data that is fed into them needs to be protected as well.
Some digital wallets use NFC cards as secure storage.
Exploring security vulnerabilities in NFC digital wallets
NFC-based devices, such as mobile digital wallets, contactless smart cards, and security keys (hardware authentication devices), are exposing users to NFC vulnerabilities in encryption, replay and side-channel attacks.
4. How to prevent digital wallet fraud by educating users #
Digital wallet users can be vulnerable to fraud if they are not aware of the risks and how to protect themselves. Take steps to educate users about the risks and how to mitigate them.
Alerting users about risks #
One way to educate users is to show alerts when they are interacting with external applications, like DApps (Decentralised Applications). DApps can be malicious and attempt to steal users’ information or funds.
The alert message warns the user that they are interacting with an external application, so they need to be cautious.
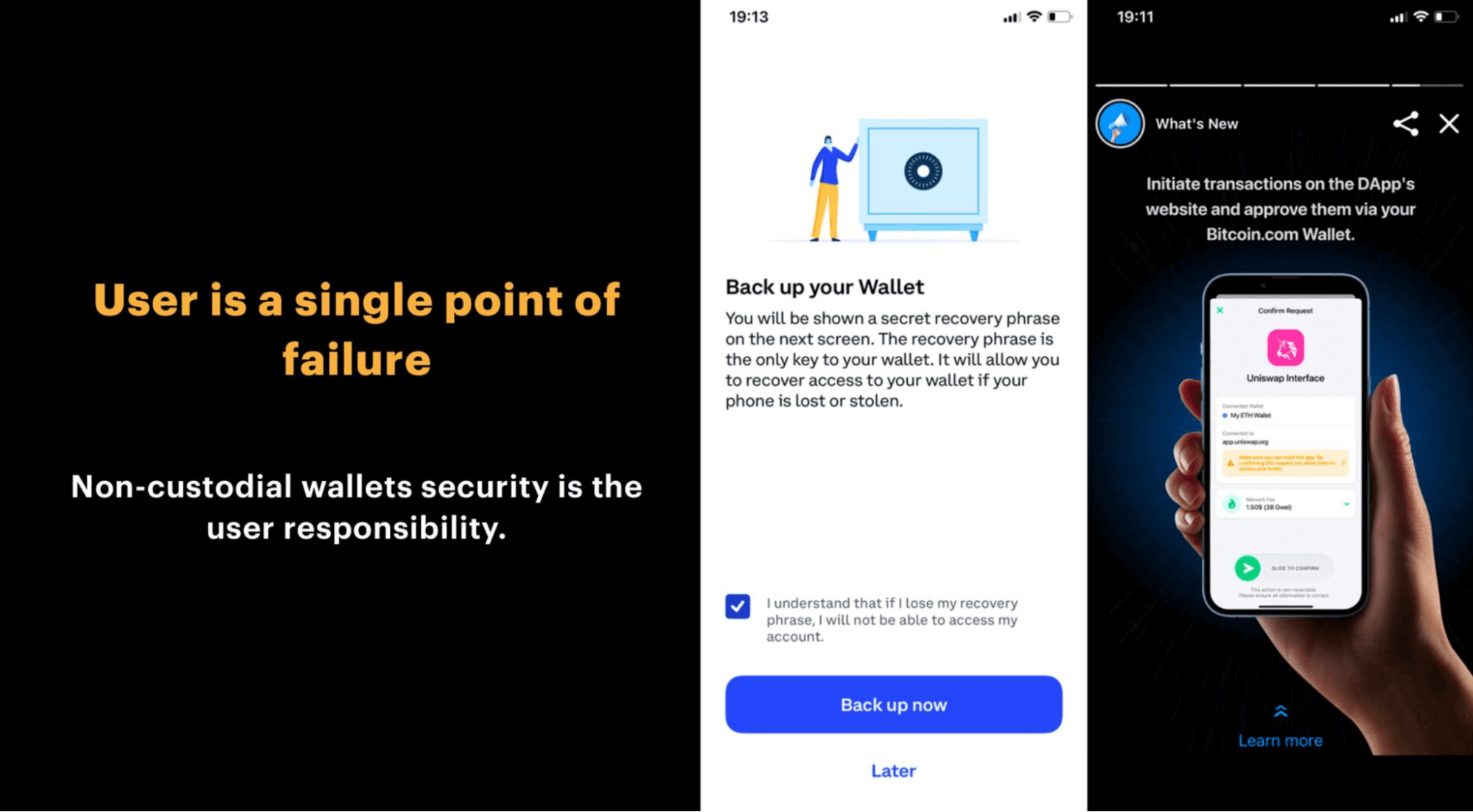
In non-custodial digital wallets the users are solely responsible for the safety of their secrets. A screenshot from a talk by Julia Mezher Crypto wallets security: for developers.
Requiring step-up authentication #
Another way to educate users is to require additional authentication before sending transactions: the user taps a button or enters a code to confirm the transaction. Additional authentication encourages the user to double-check the transaction details before sending funds. This can help prevent accidental or fraudulent transactions.
These steps help users to understand the risks and protect their wallets.
5. Anti-fraud measures: Understanding trade-offs #
Developing effective anti-fraud measures is a trade-off game between usability and security:
- Follow the user: Effective anti-fraud system is about creating controls that are user-friendly, easy to understand, and intuitive.
- Balance the trust: Each suspicious event from the user side should affect the user’s level of trust, while the system should not block the user who performed a not harmful but suspicious action unintentionally.
- FAR vs FRR: Remember about false positives and false negatives. No anti-fraud system is perfect, your goal is to continue polishing events and scores to reach the balance.
- Insider threat: The system should be protected from malicious insiders and unintentional misconfiguration.
6. How to work with security researchers #
Digital wallet fraud can result in significant financial losses and reputational damage. One of the most effective ways to prevent fraud is to work with security researchers, as they can identify security vulnerabilities and provide recommendations for improving the security of digital wallets.
There are different ways to work with security researchers: perform regular security assessments, run a bug bounty program, and have a vulnerability disclosure policy.
A bug bounty program is a way to incentivize security researchers to find and privately report vulnerabilities in a digital wallet. MetaMask has a bug bounty program in place that offers rewards of up to $50,000 for the discovery of critical vulnerabilities.
A vulnerability disclosure policy provides clear instructions on how to report a vulnerability, what information to include in the report, and how the report will be handled.
Configuring a security.txt file and including it in the app’s root directory makes it easier for security researchers to find vulnerability disclosure policy. The file provides information on how to report a vulnerability and whom to contact. Inside iOS applications, the community suggests using a security.plist file.
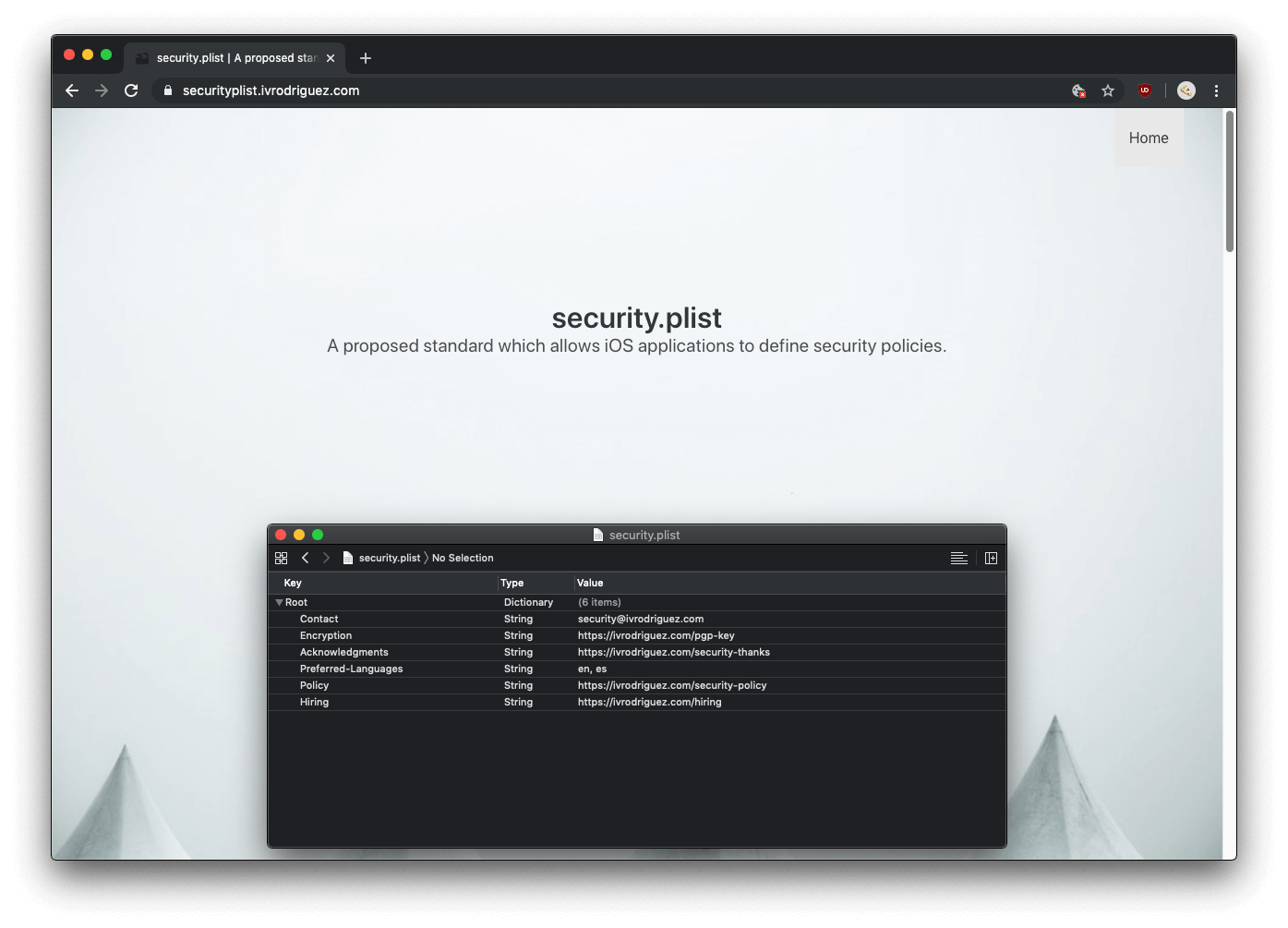
security.plist on iOS is suggested by Ivan Rodriguez.
7. Conclusion #
Building an effective anti-fraud system is crucial to protect both businesses and consumers from financial losses and reputational damage. This problem calls for a holistic approach to ensure that every aspect of financial operations is protected against potential threats.
To build an effective anti-fraud system, businesses should focus on implementing security measures for detecting and preventing fraud incidents. Building an anti-fraud system requires a multi-layered approach: strong authentication methods, gathering and analysing data from mobile apps and backend, remote device attestation, educating users and working with security researchers.
Consulting with security engineers can help businesses identify potential risks and develop a comprehensive anti-fraud strategy that aligns with their business goals and focuses on their specific digital wallet.
This blogpost is a part of the “Digital wallet security guides”: Read the articles Crypto wallets security as seen by security engineers, Exploring security vulnerabilities in NFC digital wallets, Digital payments security architecture guide.


